.svg)
Login
I audited a codebase recently for a client. Their CI/CD pipeline was beautiful. They had Snyk running SAST. They had Dependabot for SCA. All indicators were green. Zero critical vulnerabilities found. "We are secure," the Lead Dev told me.
I didn't use a buffer overflow. I didn't inject SQL. I simply manipulated the workflow. I added an item to the cart, intercepted the request, changed the quantity to -1, and proceeded to checkout. The logic subtracted the price from the total. The code syntax was perfect — so SAST missed it. The libraries were up to date — so SCA missed it. But the business logic was flawed.
Traditional scanners (SAST/DAST) are syntax checkers. They look for patterns inside the code — like eval() functions or unsanitized inputs. But they don't understand what the code is supposed to do.

These aren't coding errors. They are logic errors. The scanner sees a valid payment function processing correctly. A hacker sees a way to skip the payment step entirely. And until now, only expensive human pentesters — charging €5k/week — could find them.
At CybeDefend, we believe the future of AppSec isn't finding more syntax errors — it's understanding context. We are building the industry's first Business Logic Security Analysis (BLSA) engine.
By using Agentic AI workflows, our scanner doesn't just read code — it "understands" flows:

We are moving from "Static Analysis" to Intelligent Analysis. Not just reading code — reasoning about what it's supposed to protect.
Ignoring these flaws isn't just a security risk — it's a financial decision. Fixing a vulnerability in production costs 60× more than fixing it in development. If you wait for a pentester to find a logic flaw in production, you've already paid for the pentest (€10k+) and the remediation cost.
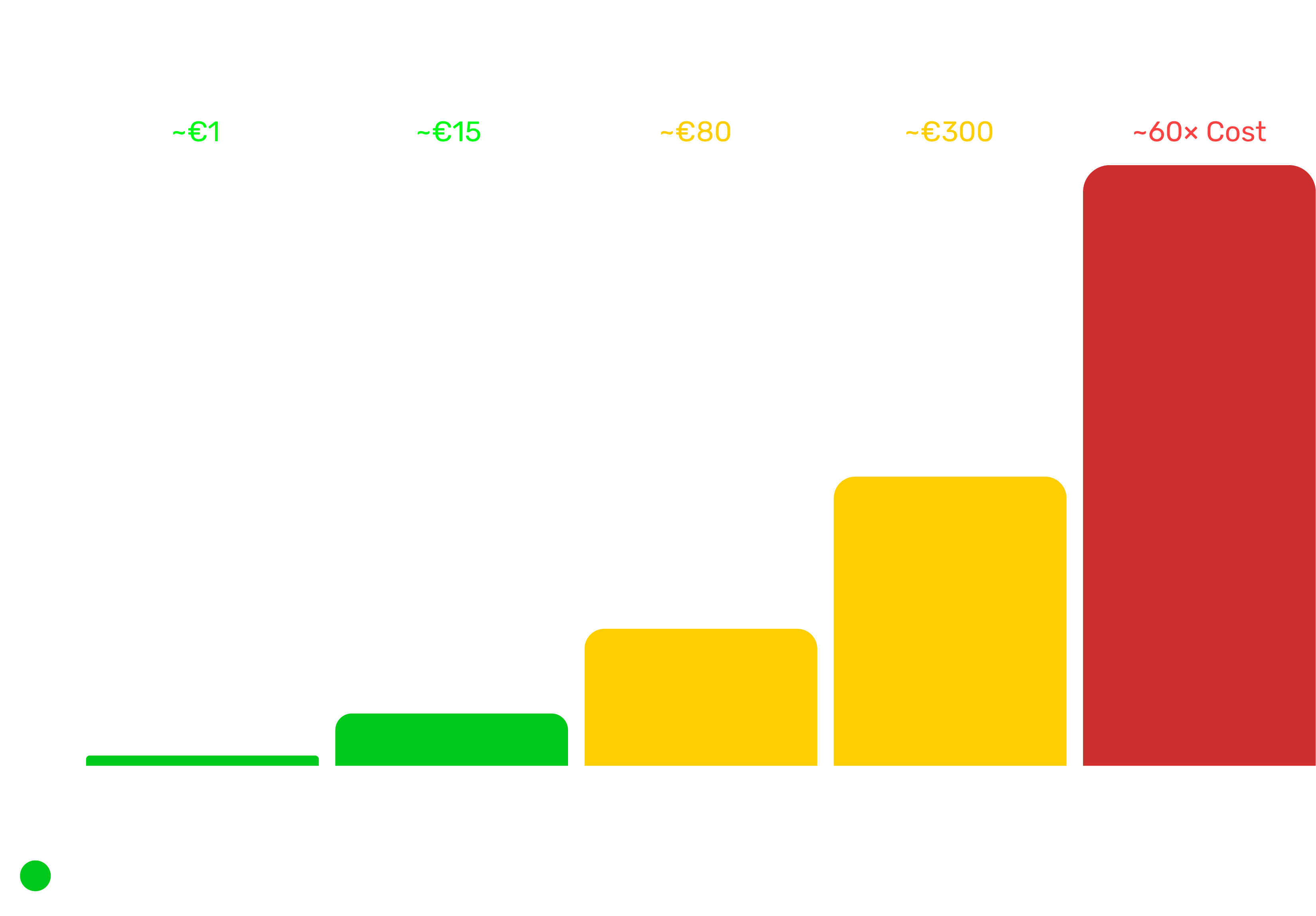
If you catch it in the PR with an automated tool? It costs you €0. If it reaches production — you're paying for the incident response, the hotfix, the downtime, and the customer support tickets. And that's before you budget for the pentest you should have done earlier.
While our full BLSA release is in Alpha, here's what every engineering team should do right now: